Secure Boot and TPM2.0
Just as Neo had to hide behind a pile of obsolete hardware to stay invisible to the machines, we could soon find ourselves forced to run on legacy boxes just to avoid a locked‑down boot chain. The good news is that the lock isn’t welded shut yet.
One day, those of us who care about digital freedom will look back at today and ask: what went wrong?
We're in a time now when terms like Secure Boot and TPM2.0 (Trusted Platform Module version 2) are common. Actually, it's a trio. We have to lob Bitlocker in there with the other two. They have been more or less standardized since 2015-2016 (though the full trifecta was made mandatory with the requirements of Windows 11 in 2011), on consumer hardware.
Like my Personal Computer - and yours.
It's everywhere. It's in every new desktop and laptop computer sold today. And on the face of it - they are good things to have. Right?
Right?
Sure. They are great things. They keep us secure and trusted. It's in the names - why would this not be so?
Well. To abandon the (increasing) conspiratorial tone for a moment, let's agree that the idea with Secure Boot and TPM is great.
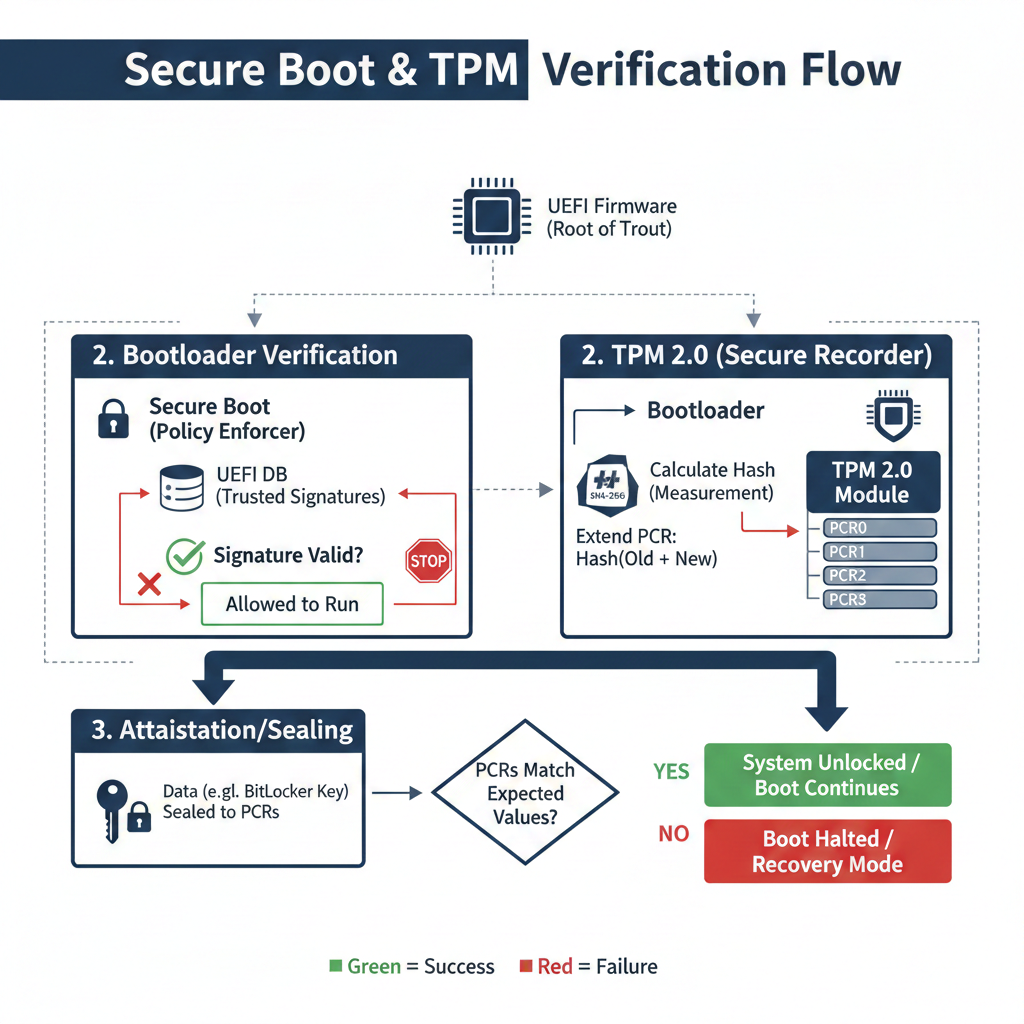
The base function for Secure Boot is to check the signature of every boot component (bootloader, kernel, drivers). If the signature matches, the firmware (UEFI) hands the control to that component. Your system boots. That's great, huh? Yes - we all agree this is excellent.
TPM2 offers a secure, non-volatile storage for cryptographic keys and can record measured-boot hashes. This can (and is) utilized to give Bitlockera hardware-bound key that is released only if the measurements match the expected Secure Boot state.
In short; Secure Boot talks to your installed bootloader, kernel and hardware drivers and checks if they have the right codes, then it checks for TPM2.0 to release system encryption, which is only released when the measured boot chain is intact.
This way - you can be sure that your operating system is indeed green-lit by whoever is deciding these things for you. On your bought and paid for system.
Anyways. As it is now, the TPM2.0 and Secure Boot work in tandem, and they rely on a predefined list of operating system codes. A list of "access codes".
If your operating system has a code in the TPM2, Secure Boot will allow it to run on your system.
This is the great part. What I just wrote.
And this idea is great.
However. We have to scrutinize this a little bit.
First, which operating systems are on the list ?
Any guesses?
Yes. Microsoft.
That's the list.
If you're like me, running Linux on your system, you can still use Secure Boot and TPM2.0.
You know why? Because Microsoft allows us.
We are allowed to use a "fallback key". Or at least most major Linux distros are allowed.
The fallback key is also called a shim or Microsoft UEFI CA, if you want to look it up.
So, we are "permitted" to use Linux with Secure Boot.
“Microsoft does not leave the door wide open for every operating system. What it does is ship a trusted certificate (the Microsoft UEFI CA) with virtually every consumer PC. Linux distributions obtain a shim that is signed by that certificate, which lets the firmware hand control over to the shim even when Secure Boot is enabled. The shim then loads the real Linux kernel only after the user (or the distro) has enrolled a second key. In short, Microsoft provides a convenient, standards‑compliant path for Linux, but the ability to boot a non‑Microsoft OS still depends on the OEM’s firmware configuration and the user’s willingness to add or manage keys.”
For now.
I've spoken about this before, and I suspect I will do so until I one day will just say "told you so".
With the increase of governmental (?) focus on control and "age verification / age assurance", we are now at last sensing where this can go.
The latest (at point of writing) is the CA AB1043, especially under Section 1798.501 proposes a clause that forces any consumer operating system to ship with a state-approved-age-verification-system.
And while I can see a plethora of issues with that alone - here's where my mind went...
Given this recent STRONG push for age verification on all sorts of online accounts (which isn't necessarily a bad idea in itself) and the new demand that every operating systems should have age assurance built in - the GNU/Linux user group experienced a collective need for head scratching.
There's no other "accounts" on a Unix/Linux based system than the local account. Only verified by the local administrator on that device.
So, besides the inane clarification given in the CA AB1043 - it makes no real sense for the *nix users at all. The only way to enforce an age verification into any operating system is through an online account, governed by a back-end like Microsoft's Entra
But GNU/Linux is open source, free and local. It never relied on remote authentication.
So, where does this lead?
Well, to maintain the control that politicians and leaders hunger for in (and is evident by) the centralized account authentication - they have to strike a deal with the manufacturers of motherboards and computer components - and restrict boot absolutely to only Windows.
(Or Mac, but they have their own "walled garden" that ensures you only boot their operating system on their hardware. Re: iPhone and iMac)
So, how can they achieve this?
Well, by making Secure Boot and TPM2.0 default, not an option - permanently enabled.
Let's re-phrase it...
If a government (or multiple) simultaneously mandates that Secure Boot and TPM 2.0 must be enabled on every device sold and requires every OS to provide a state‑approved age‑verification module, then the path of least resistance for OEMs is to ship a Windows‑only platform
At least for consumer equipment.
I am quite sure that any government official and/or contractor with enough influence could get an array of computers with ... less strict regulations.
But the control would be almost complete - for the entire world.
All of population bound to a select set of operating systems, which can only run pre-defined programs. No more freedom, no more privacy - no more personal choice.
It struck me, while I was attempting to sleep, that this reminds me of a comparison and a thought I had in the early 2000's.
I was watching "The Matrix" and I remember thinking; "why does Neo use all this deprecated hardware?"
Even for 1999 (release year) - his "hacker dungeon" looked dated and built of scraps.
Today it dawned on me.
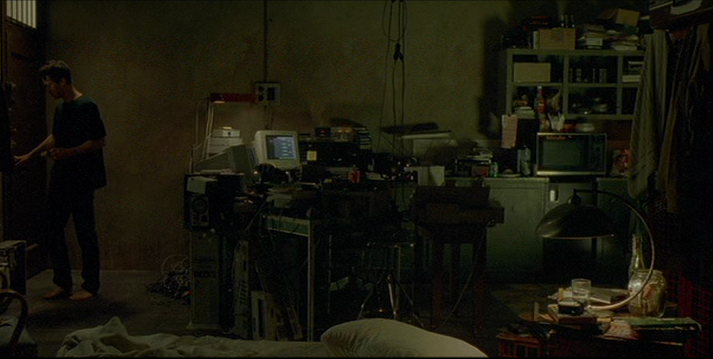
In the cyberpunk dystopia that "The Matrix" is inspired by - no one has a choice if they buy new hardware. There are too many regulations. Too many "Secure Boot and TPM2s".
To do what Neo is evidently doing - he has to rely on outdated tech, which can't be traced and isn't "predefined" by any corporation.
We are heading to a future where there's tiers of citizens. Tiers of humans.
Those with the money and influence to choose.
and us, the ones that will have to abide.
I see a potential future where Linux and "choice" is banned for people globally. And the only real choice left for us is "which hosted virtual computer should I rent".
However, for the higher echelon - the choice is more broad. I am sure.
If you made it through this rambling post - congratulations.
I can assure you it was written on much to much coffee and far too little sleep. But I couldn't let it be.
If you consider this to be incoherent conspiracy talk - you're welcome to. I often wonder that myself.
But if you have a slight sense of unrest while watching the connections and the dots... speak up. Spread what incentive you can. To investigate, speculate and consider.
I know I do. I speculate and consider far more than I spread the urge to look deeper into things like this. I think, honestly, that people with far more experience and expertise would be preferential to my ramblings.
Just as Neo had to hide behind a pile of obsolete hardware to stay invisible to the machines, we could soon find ourselves forced to run on legacy boxes just to avoid a locked‑down boot chain. The good news is that the lock isn’t welded shut yet.
Remembering my feelings from the early 2000s, I watched The Matrix, and kept wondering why Neo was hunched over a pile of **old, unbranded hardware**. At the time I thought it was a cool aesthetic, a visual "feeling".
Now it feels more like a prophecy: a world where new hardware is a sealed box, and the only way to stay free is to hide behind obsolete machines that lack the very security features that were meant to protect us.
That dystopia isn't inevitable, but it is technically feasible.
The power to keep our PCs and laptops open, hackable and genuinely ours still rests in our hands - and in the few clicks we make on the UEFI screen.
Stay curious, keep your keys under your own control, and remind the people who write the laws that digital sovereignty is a right, not a luxury.
Further Reading & Sources
- Microsoft Secure Boot Overview – https://learn.microsoft.com/en-us/windows-hardware/design/device-experiences/secure-boot-overview
- Ubuntu Secure Boot Guide – https://ubuntu.com/blog/secure-boot
- TPM 2.0 Primer – https://csrc.nist.gov/pubs/sp/800/155/ipd
- California AB 1043 (2025) – Full Text – https://legiscan.com/CA/text/AB1043/2025
- coreboot – Open Source Firmware – https://www.coreboot.org/
- Electronic Frontier Foundation – “The Right to Repair & Open Firmware” – https://www.eff.org/issues/open-firmware